In my previous blog, I covered the essentials of data sovereignty as a data protection concern for security professionals across domains.
Data protection and digital trust will be paramount in the future due to data sovereignty and regulatory compliance mandates. As the Internet of Things (IoT) expands exponentially, the resultant security and privacy risk nexus further requires a holistic approach to data protection centered on both personal and enterprise data protection strategies.
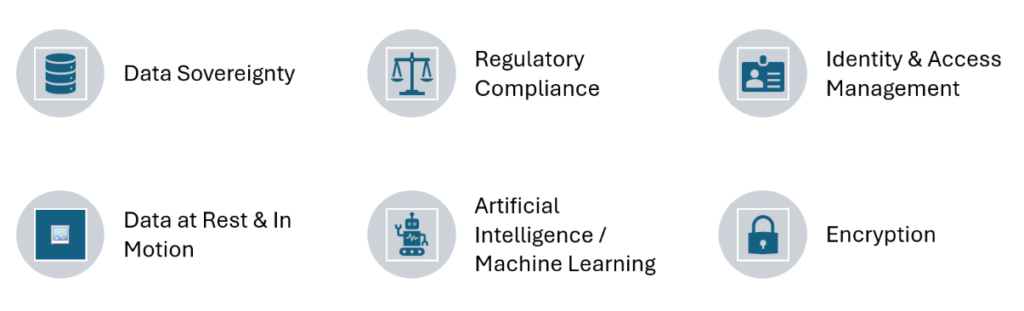
These macro business drivers will require strategies and techniques based on the following pillars to assure robust future data protection and privacy safeguards.
Let’s take a closer look:
Data sovereignty
A growing trend with data sovereignty is that cross-border data transfers will be controlled by countries to better protect privacy. As a result, global companies will need to address intricate multijurisdictional regulations and data privacy laws spanning countries.
Regulatory compliance
The rise of data sovereignty will promulgate rigorous new global data privacy laws. So,naturally data protection authorities will ramp up enforcement and levy major fines and penalties for non-compliance. Thus, companies will have to focus on building integrated security and privacy programs bolstered by the appropriate administrative, physical, and technical safeguards. As a result, security and privacy officers will have to foster a culture of security and privacy across the enterprise to leverage the “human firewall” as the first line of defense.
Identity & access management
The premise of “Identity is the Digital Perimeter” will continue to be the cornerstone for secure delivery of digital applications and services via the cloud especially due to remote / hybrid work environments. Lets look at how this maps to the two different sub-domains below.
Identity assurance
An interesting paradox is that unique multimodal biometric factors (e.g., eyes, fingerprints, facial recognition, voice, DNA) will gain in adoption for identity assurance. These must be complemented by deployment of appropriate and comprehensive privacy and security mechanisms to balance the risk.
Self-sovereign identity is a strategic macro trend in Identity Management. SSI leverages a blockchain framework for identity assurance to foster protection of identity and digital credentials while minimizing the risk of individual identity theft. An SSI personal digital passport would allow individuals to tightly control their personal data and securely sign up for digital services.
Zero trust
Zero trust tools and techniques will bolster identity as the digital perimeter for robust perimeterless data protection in the future. Zero trust requires constant validation of user identity, device posture and session risk to ensure access based on least privilege. Further, effective deployment of zero trust requires data flow mapping and business process reengineering to foster minimum necessary access.
Zero trust microsegmentation limits lateral movement by threat vectors and diminishes the enterprise attack surface. Zero trust network access (ZTNA) also enables switching from legacy device-based virtual private networks ( VPN’s) which are prone to exploits. ZTNA can help ensure delivery of secure and scalable remote access to enterprise applications and services. SASE, a coalition of network and security services, will also further extend zero trust to strengthen security across the extended enterprise in the modern digital era.
Data at rest and in motion
Organizations need to adopt a holistic, data centric, zero trust security strategy to comprehensively protect both cloud and on-premises data. The focal points are data classification, access controls, data loss prevention (DLP).
A foundational data security posture management (DSPM) platform which provides advanced analytics, encryption, access management, event reporting, and incident response features is pivotal. Further, a robust data governance program is fundamental for both traditional data sets as well as AI models. Especially for embedded AI data this is particularly important to eliminate bias.
A comprehensive certificate lifecycle management program can help to secure data in transit to strengthen ZTNA and SASE.
Artificial intelligence (AI) and machine learning (ML)
Artificial intelligence (AI) and machine learning (ML) can automate critical activities such as data discovery, classification, and access control. This can help increase efficiency, enhance security, and free up IT and security teams to focus on business value added tasks. Further, AI/ML can detect anomalous data patterns and user behavior thus helping detect threat vectors, facilitating speedier, intelligent incident response and enabling proactive breach prevention.
AI/ML can assure “minimum necessary” data collection and storage, enforcing the key precept of data minimization called for by privacy regulations. AI/ML can also automate compliance monitoring and data protection/privacy enforcement tasks. AI/ML can also be leveraged to predict data vulnerabilities and risks that may occur in the future based on historical data trend analysis.
AI can also help bolster identity assurance by detecting anomalous user behavior and usage patterns while validating trusted presence. This helps strengthen identity and access management for data stores whether in premise or cloud. It can also serve as a beacon and early warning system for untrusted or malicious actors who may have infiltrated the enterprise or external fraud attempts.
Encryption
As data becomes more mission critical, there will be a vital need to harness enhanced encryption and anonymization to protect sensitive data.
Also, with quantum computing on the horizon it is extremely important to develop and deploy computing algorithms that can combat and repel quantum threats. Homomorphic encryption is an emerging trend for securing data in the quantum computing era.
Conclusion
The data sovereignty imperative necessitates that global organizations balance data protection while fostering innovation and corporate expansion. There is a clarion call across privacy regulations for a commitment to data minimization during collection and retention.
Fostering a culture of privacy across the enterprise ecosystem along with periodic, recurring training and awareness activities can help businesses to stay ahead of the curve in their data protection efforts.
If you’d like to learn more about data sovereignty, check out this episode of the Security Visionaries podcast with Michael Dickerson, who is helping to build Australia’s first indigenous sovereign cloud.




 Indietro
Indietro 















 Leggi il blog
Leggi il blog